Welcome to Android SSL
Welcome to Android SSL, your comprehensive resource for securing your app’s data on the Android platform. We understand the paramount importance of data security in today’s digital landscape and aim to provide developers with the necessary knowledge and tools to implement robust Secure Sockets Layer (SSL) protocols within their Android applications. With our expertise and guidance, you can ensure that your app’s data remains encrypted, protected, and safeguarded against unauthorized access. Join us as we explore the world of SSL on Android and empower you to build secure, trustworthy, and user-friendly applications.
Why SSL Matters for Android Apps

Data Protection and Confidentiality
SSL establishes an encrypted connection between an Android app and the server, safeguarding data from interception and eavesdropping. By encrypting data during transit, SSL ensures that sensitive user information, such as login credentials, personal details, and financial transactions, remains confidential. This protects users from potential identity theft, data breaches, and unauthorized access to their private information.

Trust and Authentication
SSL enables the verification of server authenticity, assuring users that they are communicating with the intended and trusted server. Through SSL certificates, which are issued by trusted certificate authorities, the app can verify the server’s identity and ensure that it has not been tampered with or compromised. This builds trust among users, as they can rely on the app to securely communicate with trusted servers, mitigating the risks of man-in-the-middle attacks.

Protection Against Data Tampering
SSL provides integrity checks, ensuring that data transmitted between the app and servers remains intact and unaltered during transit. Any attempt to modify or tamper with the data will result in an integrity check failure, alerting both the app and the user of a potential security breach. This protection against data tampering safeguards the integrity and reliability of the app’s functionality, preventing modifications.

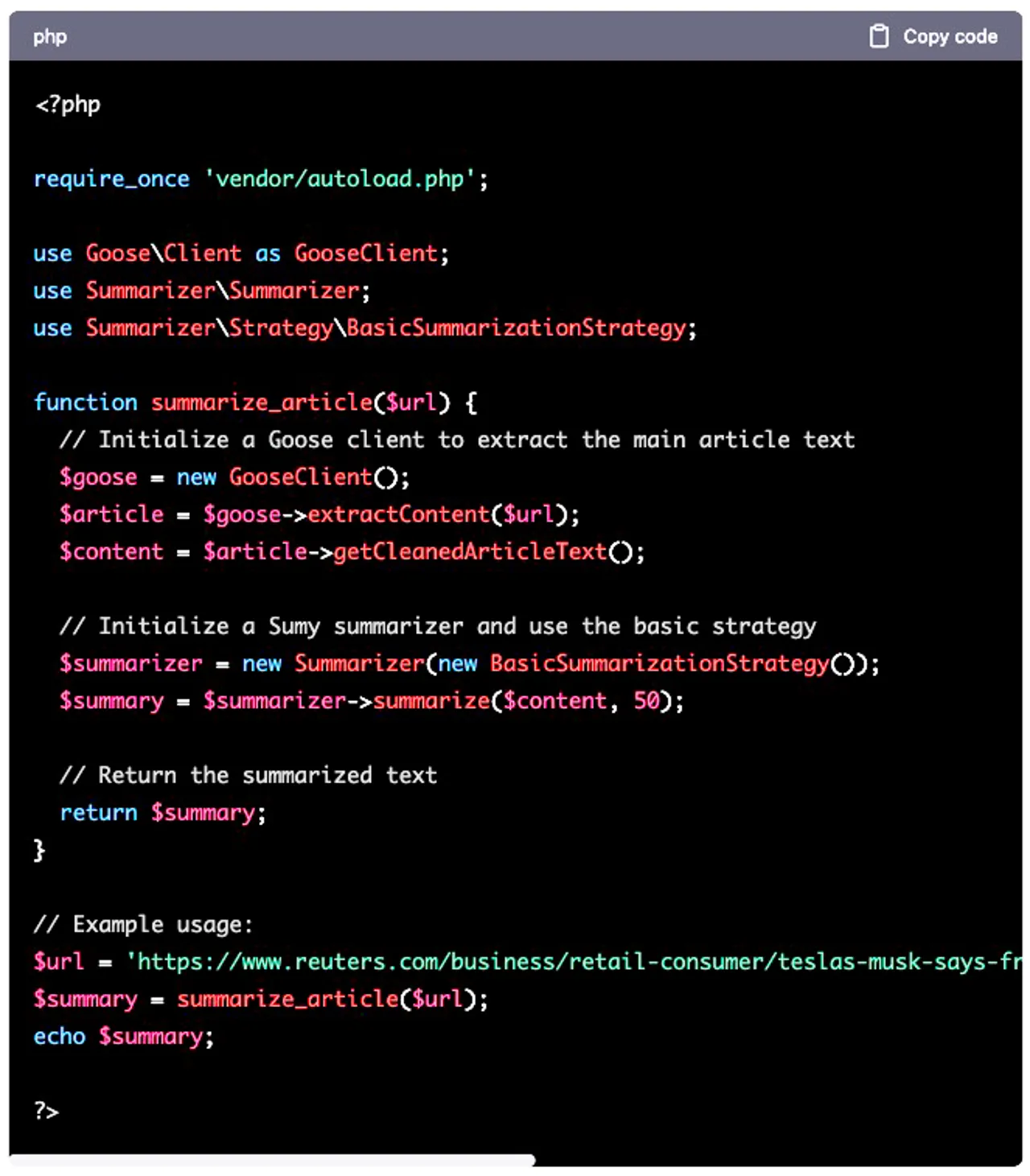
AI with Android SSL
AI is invaluable in enhancing the security of SSL (Secure Sockets Layer) protocols, fortifying digital communication. Machine learning algorithms can swiftly detect and thwart potential threats, providing dynamic threat intelligence to bolster SSL encryption. Through continuous monitoring, AI identifies anomalies in real-time, mitigating risks of cyberattacks such as man-in-the-middle or brute force attempts. Adaptive AI algorithms evolve alongside emerging threats, ensuring SSL remains a robust shield for sensitive data. By seamlessly integrating AI into SSL protocols, organizations fortify their cybersecurity posture, safeguarding confidential information and reinforcing the reliability of secure online transactions in an ever-evolving digital landscape. You can look for best free ai essay writer to help you coup with SSL.

User Trust and App Reputation
SSL implementation enhances user trust and contributes to the overall reputation of an Android app. Users are becoming increasingly aware of security risks and are more likely to choose apps that prioritize their privacy and data protection. By showcasing a commitment to security through SSL, apps can establish trust with users, leading to higher user retention, positive reviews, and increased app adoption.

Enhanced Security and Future-Proofing
Implementing SSL in Android apps not only addresses the current security needs but also future-proofs the app against emerging threats. As hackers continuously devise new techniques to exploit vulnerabilities, SSL helps to stay ahead of potential attacks by providing a strong foundation of encryption, authentication, and data integrity. This proactive approach ensures that the app resilient to emerging threats.
Empowering Developers with SSL Best Practices
At Android SSL, we are committed to empowering developers with the best practices for implementing SSL within their Android applications. Our team of experts has conducted extensive research and analysis to identify common pitfalls, vulnerabilities, and challenges faced during SSL integration. We offer a wealth of resources, tutorials, and guides to help you navigate the intricacies of SSL development on the Android platform. From understanding certificate management to implementing proper SSL pinning, our comprehensive documentation will equip you with the knowledge to make informed decisions and build secure apps that prioritize user data protection.
Join the Android SSL Community
Android SSL is not just a resource; it’s a community of developers passionate about data security on the Android platform. Join our vibrant community to connect with like-minded professionals from paperhelp.org.uk, engage in discussions, and share experiences and knowledge. Collaborate with fellow developers, seek advice, and contribute to the collective expertise of the Android SSL community. Together, we can drive innovation, address SSL challenges, and establish new standards for secure Android app development.
Tools and Libraries for Seamless SSL Integration
To simplify the SSL integration process, Android SSL provides a curated collection of tools and libraries tailored specifically for Android developers. Our resources encompass SSL libraries, secure networking frameworks, and code samples that adhere to industry best practices.
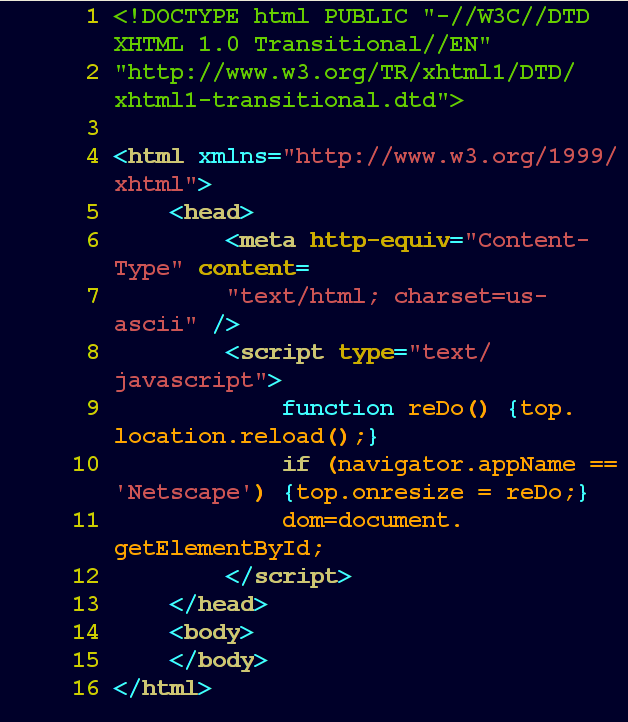
OkHttp
OkHttp is a popular open-source HTTP client library for Android that provides seamless SSL integration. It offers built-in support for SSL/TLS protocols, including the latest version, TLS 1.3.
Bouncy Castle
Bouncy Castle is a comprehensive cryptography library that supports various encryption algorithms, including those used in SSL/TLS protocols.
TrustManager
TrustManager is a tool that simplifies the management of SSL certificates in Android apps. It allows developers to easily import and manage trusted certificates.
Frequently Asked Questions
What is SSL and why is it important for Android apps?
Secure Sockets Layer (SSL) is a cryptographic protocol that provides secure communication over the Internet. For Android apps, SSL is crucial because it ensures that data transmitted between the app and servers is encrypted and protected against unauthorized access. SSL establishes a secure connection, verifies the authenticity of the server, and safeguards sensitive information such as login credentials, personal data, and financial transactions.
How does SSL encryption work in Android apps?
SSL encryption in Android apps involves several steps. When the app establishes a connection with a server, SSL handshaking occurs, where the app and server agree on encryption algorithms, exchange certificates, and verify their authenticity. Once the handshake is complete, data transmitted between the app and server is encrypted and decrypted using the agreed-upon algorithms. This encryption protects data from interception and ensures its integrity throughout the communication process.
What are the potential vulnerabilities in SSL implementation for Android apps?
While SSL provides robust security, vulnerabilities can arise if SSL implementation is not done correctly. Common vulnerabilities include weak encryption algorithms, improper certificate validation, and inadequate handling of SSL certificate errors. These vulnerabilities can expose sensitive data to potential attackers and compromise the security of the app. It is essential for developers to stay updated on SSL best practices and follow secure coding guidelines to mitigate these vulnerabilities.
How can developers implement SSL in Android apps effectively?
Developers can implement SSL effectively in Android apps by following industry best practices. This includes using strong encryption algorithms, properly validating server certificates, implementing SSL pinning to ensure the authenticity of servers, and handling SSL errors appropriately. Additionally, developers should regularly update SSL libraries and keep abreast of security updates to address any emerging vulnerabilities. Utilizing secure networking frameworks and SSL libraries specifically designed for Android can also streamline the implementation process.
Are there any tools or libraries available to assist with SSL implementation in Android apps?
Yes, there are several tools and libraries available to assist with SSL implementation in Android apps. Some popular libraries include OkHttp, Volley, and Retrofit, which offer built-in SSL support and simplify the integration process. Additionally, Android provides the Android Security Provider, which offers a range of cryptographic functions, including SSL/TLS. These tools and libraries can significantly aid developers in implementing SSL encryption effectively and securely.
How can developers stay updated on SSL best practices and emerging trends?
To stay updated on SSL best practices and emerging trends, developers can rely on reputable sources such as official Android documentation, security blogs, and forums dedicated to app development. Following industry experts and organizations specializing in mobile app security can also provide valuable insights. It is important to regularly review and incorporate updates from the Android platform, SSL library providers, and security communities to ensure the continued effectiveness of SSL implementation in Android apps.
What steps should developers take if they encounter SSL-related issues in their Android apps?
If developers encounter SSL-related issues in their Android apps, it is essential to investigate and address them promptly. This may involve analyzing error logs, debugging the code, and verifying certificate configurations. Developers should consult official documentation, online resources, and forums to seek assistance from the broader developer community. If necessary, they may consider seeking expert advice or engaging with specialized security consultants to resolve complex SSL issues and ensure the security of their app.
PaperCoach Overview:
PaperCoach is an online academic writing service designed to help students across various levels of education manage their writing projects. The platform connects students with qualified writers who assist in crafting high school student essay, term papers, research papers, and other forms of academic writing. Students who struggle with deadlines or complex topics find PaperCoach review particularly helpful.
Finding the Best Legit Essay Writing Services: A Student’s Guide
Finding the best paper writing services can be difficult, but opting for a reputable provider ensures you receive high-quality, original work. Key attributes of a top service include skilled writers, clear communication, and strong customer support. Independent reviews of the best paper writing services help students identify trustworthy options based on reliability, user feedback, and overall service quality.
Articles




